Firewall penetration testing
There was a problem providing the content you requested
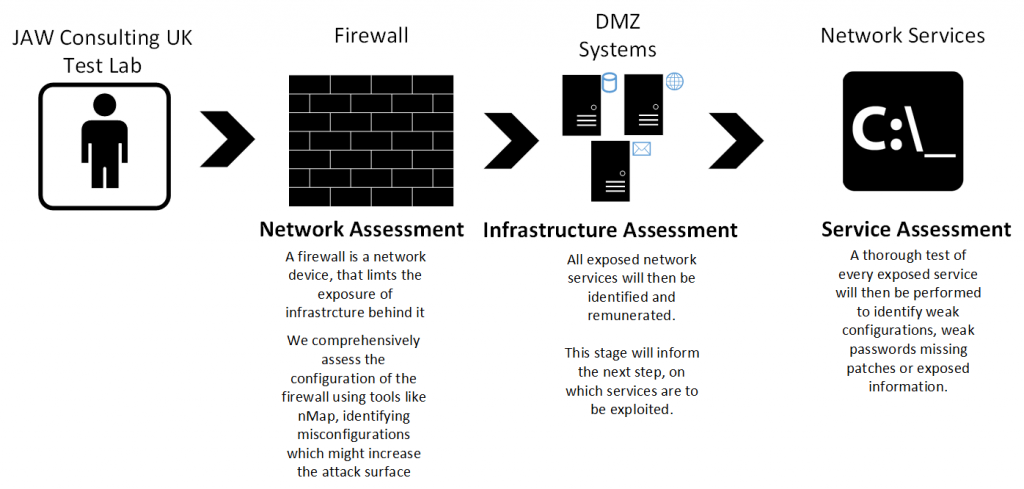
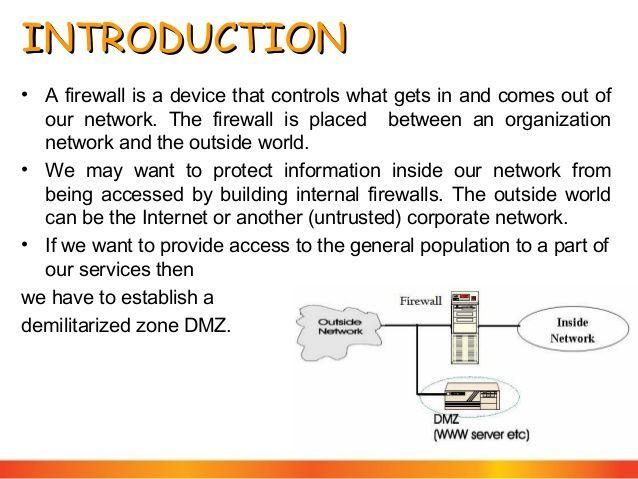
20 Jun Nettitude's Firewall Security Testing services assess the firewall from the internet to deliver real life mitigation tactics identifying potential.

www.biozdravi.eu is an online framework for penetration testing and security Even if you have all the tools on your machine, the local firewall of your network.


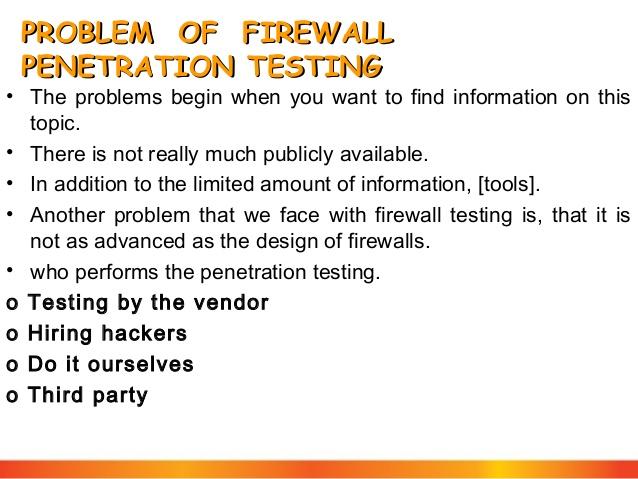


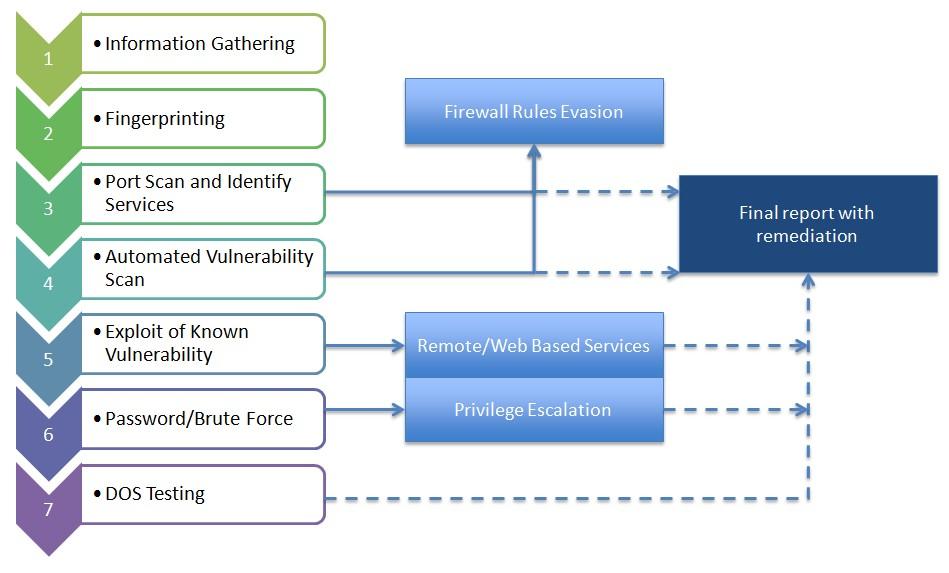
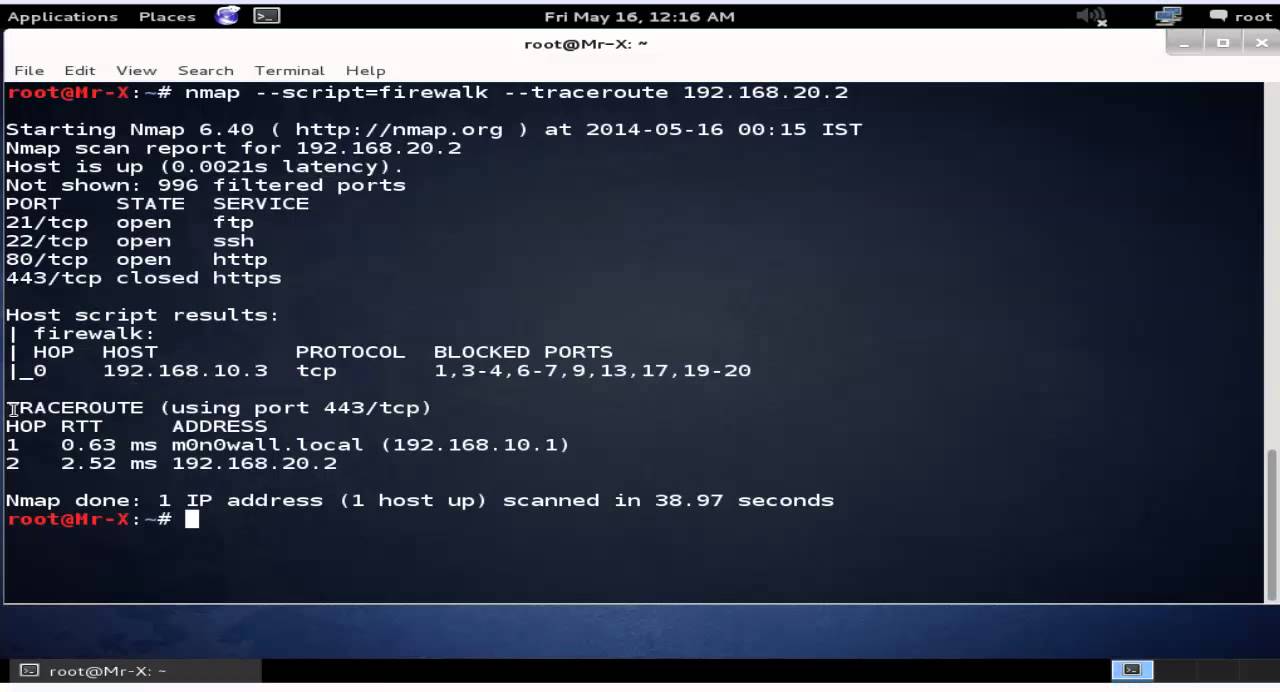

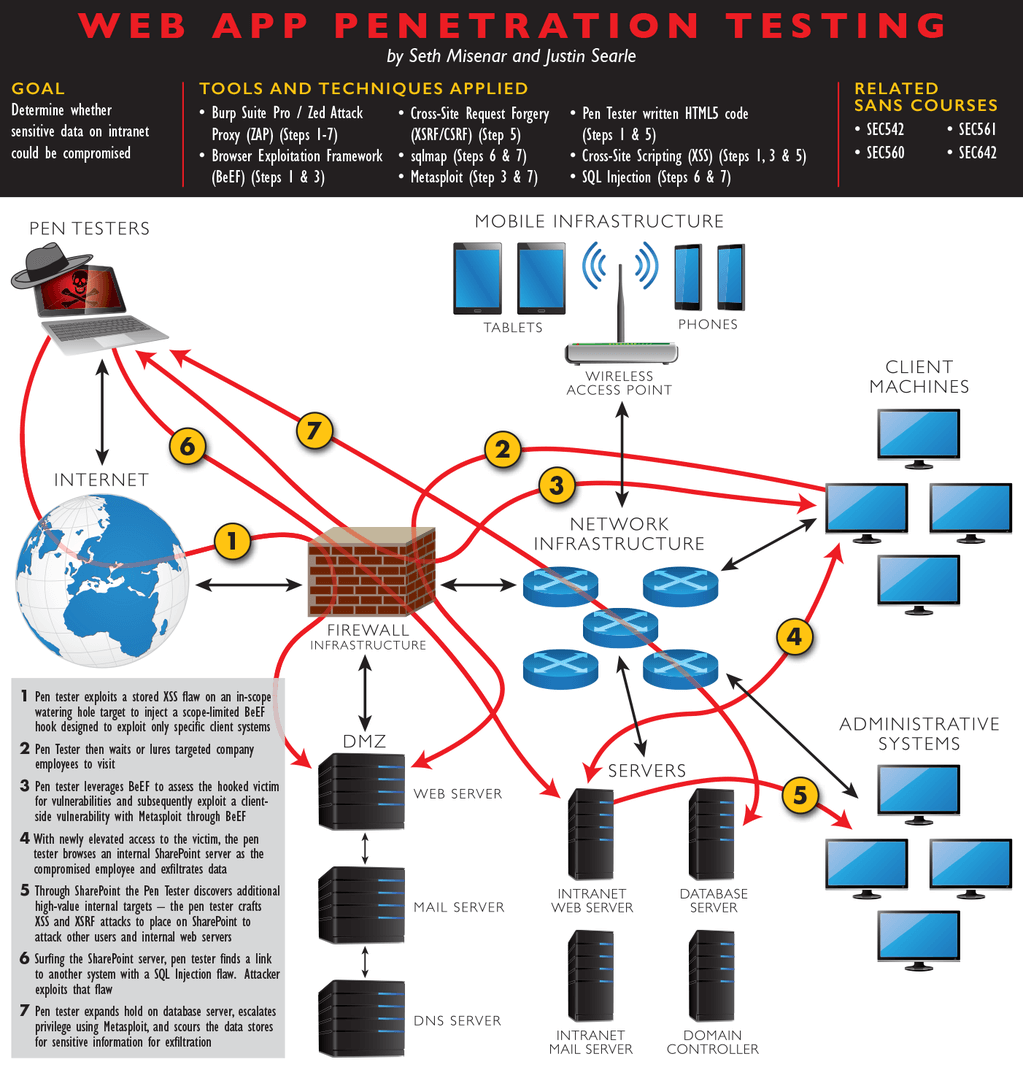

Description:Scenario Attackers are always hunting for clients that can be easily compromised and they can enter such networks with IP spoofing to damage or steal data. The attacker can get packets through a firewall by spoofing the IP address. If attackers are able to capture network traffic, as you have learned to do in the previous lab, they can perform Trojan attacks, registry attacks, password hijacking attacks, etc. An attacker may use a network probe to capture raw packet data and then use this raw packet data to retrieve packet information such as source and destination IP address, source and destination ports, flags, header length, checksum, Time to Live TTL , and protocol type. Therefore, as a network administrator you should be able to identify attacks by extracting information from captured traffic such as source and destination IP addresses, protocol type, header length, source and destination ports, etc. You can also check the attack logs for the list of attacks and take evasive actions.







































User Comments 5
Post a comment
Comment: